Multi-Factor Authentication and VPN
How to Install and Use Multi-Factor Authentication with Global Protect VPN Client on Windows:
Check with IT Services Help Desk to get assistance scanning your computer for viruses or malware, before you connect your personal system to Clark’s internal network via VPN.
The IT Services Help Desk can be reached at:
- https://itshelpdesk.clark.edu
- ithelp@clark.edu
- 360 992-2425
Overview
To protect Clark College networks and digital information, we are enabling Multi-Factor Authentication (MFA) as an additional security measure for users who connect to the Clark College Virtual Private Network (VPN). Our VPN allows faculty and staff to connect to the Clark College on-campus network via an encrypted connection. Currently users are only required to have their Clark usernames and passwords to connect to the network. This is a major vulnerability in our Information Security, and best practices are to require a third authentication requirement. We will be using the vendor OKTA to accomplish this.
What is OKTA?
Okta is the name of the vendor that Clark College will use going forward to provide secure identity verification. Moving forward you will be able to connect to your OKTA account and then have access to other accounts seamlessly, without having to remember multiple credentials. The VPN is the first service that will use OKTA for this task.
Okta Multi-Factor Authentication (MFA) Setup
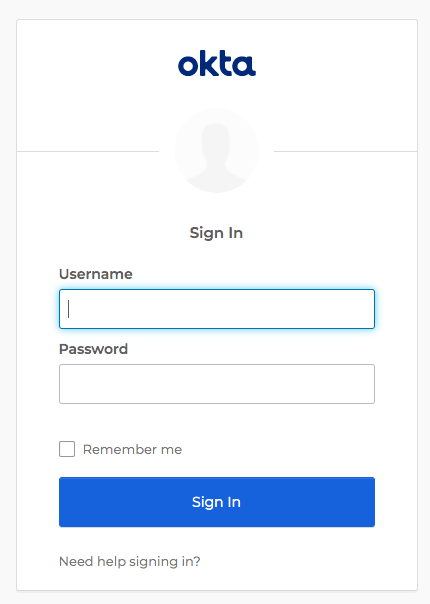
- The first time you sign into Clark VPN or https://clark.okta.com, log in using your Clark email address and Clark network password.
- You will be asked to set up multifactor authentication. Click Setup under your preferred
method:
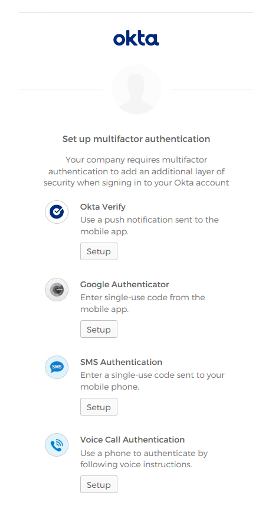
If you do not have an Authentication app like Okta Verify, or Google Authenticator installed on your mobile device, please download and install Okta Verify to your mobile device. This app is available on the Apple App Store or the Google Play Store. If you are unable to install an authentication app, please connect with IT support. - Follow the instructions to verify using your chosen app, SMS message or Phone authentication. Directions for each sign on method can be found here: Okta MFA Configuration
